Global Cyber Security Market Research Report: By Component (Solution and Service), By Deployment Model (Cloud and On-Premise), By Enterprise Size (Large Enterprises and SMEs), By Industry Vertical (Telecom, Automotive, BFSI, Public Sector, Retail, Healthcare, IT, Energy & Utilities, Manufacturing, and Others), and Region (North America, Europe, Asia-Pacific, and Rest of the World) Global Industry Analysis, Size, Share, Growth, Trends, Regional Analysis, Competitor Analysis and Forecast 2023-2031.
The global cyber security market was valued at USD 175.80 billion in 2022 and is estimated to reach approximately USD 390.80 billion by 2031, at a CAGR of 9.2% from 2023 to 2031.
Over the past few decades, the cybersecurity sector has expanded and changed dramatically. The importance of safeguarding sensitive data from cyber threats has increased as businesses and individuals rely more and more on digital technologies. In order to protect networks, systems, and data against harmful activities like hacking, malware, and data breaches, this market includes a wide range of goods and services. Stricter regulatory regulations, an increase in Internet of Things (IoT) devices, and an increase in cyberattack frequency and sophistication are major factors driving the growth of the cybersecurity industry. As a result, businesses from the financial to the medical industries allot large expenditures to cybersecurity solutions. Various products and services, including firewalls, antivirus software, intrusion detection systems, and encryption tools, are available in this sector, along with others like threat analysis, incident response, and security consultancy. As more enterprises migrate to the cloud, cloud-based security solutions have become more popular. The market is quite competitive, and there are many vendors and providers offering specialized solutions to satisfy customers' unique needs. The cybersecurity market is still dynamic and is anticipated to expand as the digital landscape enlarges and becomes more complicated. Threats are also evolving as technology progresses.
CYBER SECURITY MARKET: REPORT SCOPE & SEGMENTATION
|
Report Attribute |
Details |
|
Estimated Market Value (2022) |
175.80 Bn |
|
Projected Market Value (2031) |
390.80 Bn |
|
Base Year |
2022 |
|
Forecast Years |
2023 - 2031 |
|
Scope of the Report |
Historical and Forecast Trends, Industry Drivers and Constraints, Historical and Forecast Market Analysis by Segment- By Component, By Deployment Model, By Enterprise Size, By Industry Vertical, & Region |
|
Segments Covered |
By Component, By Deployment Model, By Enterprise Size, By Industry Vertical, & Region |
|
Forecast Units |
Value (USD Billion or Million), and Volume (Units) |
|
Quantitative Units |
Revenue in USD million/billion and CAGR from 2023 to 2031 |
|
Regions Covered |
North America, Europe, Asia Pacific, Latin America, and Middle East & Africa, and the Rest of World |
|
Countries Covered |
U.S., Canada, Mexico, U.K., Germany, France, Italy, Spain, China, India, Japan, South Korea, Brazil, Argentina, GCC Countries, and South Africa, among others |
|
Report Coverage |
Market growth drivers, restraints, opportunities, Porter’s five forces analysis, PEST analysis, value chain analysis, regulatory landscape, market attractiveness analysis by segments and region, company market share analysis, and COVID-19 impact analysis. |
|
Delivery Format |
Delivered as an attached PDF and Excel through email, according to the purchase option. |
Global Cyber Security Market Dynamics
Due to the COVID-19 pandemic's rapid digital change, people have become more dependent on online services and distant labour, which has raised the risk of cyberattacks. As a result, businesses all over the world increased their spending on cybersecurity solutions to safeguard sensitive information and maintain business continuity. Additionally, the threat landscape was changing, with more complex and persistent cyber threats like ransomware assaults, supply chain hacks, and state-sponsored cyber espionage becoming more common. The need for cutting-edge security systems, threat information, and incident response services increased as a result. The cybersecurity market was also fueled by regulatory reforms like the General Data Protection Regulation (GDPR) of the European Union and the California Consumer Privacy Act (CCPA). Due to the severe penalties for non-compliance, businesses have made data protection and privacy a top priority. As a result, the cybersecurity market expanded significantly, with more mergers and acquisitions, the appearance of creative startups, and a greater emphasis on security solutions based on AI and machine learning. Geopolitical tensions, shifting government cybersecurity agendas, and the ongoing race between cybercriminals and defenders all had an impact on the market's dynamics, making it a crucial industry in the digital era that is constantly changing.
Global Cyber Security Market Drivers
The ubiquitous availability of high-speed internet and the quick development of digital technology have made remote work more feasible and practical than before. Employees can access company resources and work from almost anywhere with the use of cloud-based collaboration tools, virtual private networks (VPNs), and secure communication platforms, which encourages the adoption of remote work and BYOD policies. Flexibility and work-life balance are valued more and more in today's workforce. Employees want the freedom to select their workplace, which has prompted businesses to adopt policies allowing remote work as a competitive advantage in luring and keeping top talent. Similar to this, BYOD supports this philosophy by enabling employees to complete work-related tasks on their chosen devices, increasing their level of job satisfaction.
Technology breakthroughs, corporate opportunities, and societal requirements all play major roles in the growth of the Internet of Things (IoT). Technology advancements are a key motivator. The ability to incorporate sensors and communication capabilities in ordinary things has become more practical as a result of the miniaturization of sensors, the fall in price of hardware components, and the growth of high-speed internet connectivity. Because of this, sophisticated hardware and software that can easily gather and transfer data have been developed. A crucial role is played by business opportunities. Businesses are aware of the potential IoT holds for generating new revenue streams, reducing costs, and enhancing consumer experiences. There are numerous market potential, ranging from wearables and smart homes to industrial IoT applications. The ability to gather and analyze data from IoT devices allows businesses to make more informed decisions, enhance operational efficiency, and offer innovative products and services.
Restraints:
Public trust has been damaged by high-profile data breaches and instances of data exploitation. People fear that if their private information is misused, it could result in identity theft, financial fraud, and other nefarious acts. People are becoming more conscious of ubiquitous tracking and surveillance devices. This encompasses both government monitoring programmes and internet tracking by tech and social media corporations. Personal freedoms can be violated if one feels continually watched. Many people believe they have little control over their personal information. Even when services have privacy settings, it can be difficult for users to control what information is shared and with whom due to the complexity and opacity of these choices. The introduction of privacy legislation might be restrictive even though they are meant to protect people. Many individuals feel they have limited control over their personal data. Even when services offer privacy settings, the complexity and opacity of these settings can make it challenging for people to manage what information is shared and with whom.
There are an increasing number of systems and solutions due to the quick development of technology. It can be challenging and time-consuming to integrate these various technologies into a cohesive ecosystem. Many organizations continue to use antiquated systems, which can be difficult to combine with more modern technologies. This results in technical debt and makes the modernization process more difficult. Modern systems are very interconnected, including cloud services and Internet of Things (IoT) gadgets. For security and performance, it is crucial to manage the interactions and relationships between these elements, which can be difficult. There are a tonne of providers and solutions in fields like cybersecurity. Effective selection, integration, and management of these varied tools can be difficult for organizations. Complex integrated systems often present vulnerabilities. Ensuring that integrated solutions meet security and compliance standards can be a daunting task. Integrating systems and managing complexity requires significant resources, including time, skilled personnel, and financial investments. This can strain budgets and divert resources from other critical areas.
Opportunities:
In order to protect sensitive data, systems, and networks, effective threat detection and prevention are now more important than ever due to the frequency and complexity of cyberattacks. A burgeoning market for cutting-edge security solutions has resulted from this. Organizations must employ efficient threat detection and prevention strategies to be compliant and avoid fines as a result of the world's stricter data protection laws. Meeting these requirements gives cybersecurity service providers more opportunities. To secure these networked systems, there is a greater demand for specialized threat detection and prevention solutions as a result of the development of Internet of Things (IoT) devices and cloud services, which has increased the attack surface. By analyzing huge information in real-time, the incorporation of artificial intelligence and machine learning into cybersecurity enables more precise and effective threat identification, opening up prospects for creative solutions.
To benefit from scalability, cost savings, and flexibility, businesses are moving their data, applications, and infrastructure to the cloud. Strong cloud security measures are now even more necessary as a result of its widespread deployment. Businesses are most concerned about data theft and breaches. Cloud security tools help protect sensitive data housed there, giving service providers a chance to fill this urgent need. There are strict data protection laws in many different sectors and places. By offering encryption, access restrictions, and monitoring tools, cloud security solutions help organizations comply with regulations like GDPR and HIPAA. The simultaneous usage of many cloud service providers by many organizations complicates security management. This situation creates possibilities for security solutions that can provide unified protection across several cloud platforms.
Segment Overview
By Component
Based on component, the global cyber security market is divided into solution and service. The solution category dominates the market with the largest revenue share in 2022. Cybersecurity solutions comprise a range of software and hardware products designed to detect, prevent, and mitigate security threats. These solutions encompass antivirus and anti-malware software, firewalls, intrusion detection and prevention systems, encryption tools, and endpoint security solutions, among others. Cybersecurity solutions are essential for safeguarding networks, devices, and data against a wide spectrum of threats, from malware to insider attacks. Cybersecurity services, on the other hand, encompass the various professional and managed services that assist organizations in bolstering their security posture. These services include security consulting, risk assessments, penetration testing, incident response, and managed security services. Service providers offer expertise, analysis, and ongoing support to help organizations navigate the ever-evolving threat landscape and ensure that their security measures are effective and up-to-date.
By Deployment Model
Based on the deployment model, the global cyber security market is categorized into cloud and on-premise. The cloud category leads the global cyber security market with the largest revenue share in 2022. Cloud-based cybersecurity solutions are hosted and operated by third-party service providers in remote data centers. These solutions are accessible over the internet and are designed to protect digital assets in cloud environments, web applications, and remote work setups. Cloud solutions are highly scalable, allowing organizations to adapt their security infrastructure to changing needs without significant hardware investments. On-premise cybersecurity solutions, in contrast, are installed and maintained within an organization's own physical infrastructure. These solutions are directly controlled and managed by the organization and are commonly used for securing internal networks and sensitive data.
By Enterprise Size
Based on enterprise size, the global cyber security market is segmented into large enterprises and SMEs. The large enterprises segment dominates the cyber security market. Large enterprises are often multinational corporations or organizations with significant resources, expansive networks, and complex IT infrastructures. Large enterprises typically have intricate IT systems and networks, often with a mix of on-premise and cloud-based solutions, making their security requirements more complex. These organizations often have substantial cybersecurity budgets to invest in advanced solutions, dedicated security teams, and ongoing training for their personnel. Large enterprises can need to adhere to numerous industry-specific regulations and compliance standards, which often require robust cybersecurity measures and reporting. SMEs are typically smaller businesses with limited resources, simpler IT infrastructures, and smaller budgets. SMEs often have limited budgets, personnel, and IT infrastructure to allocate to cybersecurity efforts. Their IT environments are generally less complex, with fewer systems and endpoints to secure. While SMEs can also be subject to regulations, they can struggle to meet compliance requirements due to resource limitations.
By Industry Vertical
Based on industry vertical, the global cyber security market is divided into telecom, automotive, BFSI, public sector, retail, healthcare, IT, energy & utilities, manufacturing, and others. The BFSI category dominates the market with the largest revenue share in 2022. The BFSI sector handles highly sensitive financial and personal data. It's a prime target for cyberattacks, making robust cybersecurity essential to protect assets, customer information, and maintain regulatory compliance. The telecom sector involves telecommunications companies and providers that manage vast networks and handle significant volumes of customer data. Ensuring network security and safeguarding customer information are paramount in this sector. As automobiles become more connected and reliant on software, the automotive sector faces increasing cybersecurity challenges. Protecting vehicle systems from cyber threats is vital to ensure safety and data privacy. Government agencies at all levels are entrusted with critical data, infrastructure, and services. Protecting national security, public records, and critical infrastructure from cyber threats is a top priority in the public sector. The retail sector processes vast amounts of customer data, including payment information. Cybersecurity is crucial to protect against data breaches and maintain customer trust. The healthcare sector manages sensitive patient information and medical devices. Protecting patient privacy, securing electronic health records, and ensuring the integrity of medical devices are cybersecurity imperatives. The IT sector includes companies that provide technology solutions and services. They require strong cybersecurity measures to protect intellectual property, client data, and infrastructure. Critical infrastructure in the energy and utilities sector must be protected from cyber threats. This includes power grids, water supply systems, and oil and gas facilities. The manufacturing sector has seen an increasing convergence of IT and operational technology (OT). Ensuring the security of production systems, supply chains, and intellectual property is essential.
Global Cyber Security Market Overview by Region
The global cyber security market is categorized into North America, Europe, Asia-Pacific, and the Rest of the World. Asia-Pacific emerged as the leading region, capturing the largest market share in 2022. Asia-Pacific has experienced rapid technological advancement, with nations like China, India, and South Korea emerging as key players in the global IT sector. Due to the speed of the digital transition, cybersecurity must now receive more attention in order to safeguard sensitive data and vital infrastructure. Online transactions, data sharing, and e-commerce activities have increased as a result of the region's developing digital economies. As a result, governments, companies, and individuals all place a high importance on cybersecurity. Asia-Pacific has had its fair share of cyberthreats, including financially driven cybercrime and state-sponsored attacks. These instances have brought attention to the necessity of strong cybersecurity measures to protect against a variety of attacks. To improve cybersecurity safeguards and safeguard individual privacy, many nations in the area have enacted or improved data protection legislation. Investments in cybersecurity services and solutions have increased as a result of these regulatory actions. For both domestic and foreign industries, Asia-Pacific has emerged as a hub. The demand for cybersecurity services and solutions has been driven by the need to protect company data, intellectual property, and customer information. Governments, corporations, and the general public are becoming more and more conscious of the significance of cybersecurity. Investments in cybersecurity initiatives, training, and education have increased as a result of this increased awareness.
Global Cyber Security Market Competitive Landscape
In the global cyber security market, a few major players exert significant market dominance and have established a strong regional presence. These leading companies remain committed to continuous research and development endeavors and actively engage in strategic growth initiatives, including product development, launches, joint ventures, and partnerships. By pursuing these strategies, these companies aim to strengthen their market position, expand their customer base, and capture a substantial share of the market.
Some of the prominent players in the global cyber security market include BAE Systems Plc; Broadcom, Inc.; Centrify Corp.; Check Point Software Technology Ltd.; Cisco Systems, Inc.; FireEye, Inc.; Fortinet, Inc.; International Business Machines Corp.; Lockheed Martin Corp.; LogRhythm, Inc.; McAfee, LLC.; Palo Alto Networks, Inc.; Proofpoint, Inc.; Sophos Ltd.; Trend Micro Inc. , and various other key players.
Global Cyber Security Market Recent Developments
Scope of the Global Cyber Security Market Report
Cyber Security Market Report Segmentation
|
ATTRIBUTE |
DETAILS |
|
By Component |
|
|
By Deployment Model |
|
|
By Enterprise Size |
|
|
By Industry Vertical |
|
|
By Geography |
|
|
Customization Scope |
|
|
Pricing |
|
Objectives of the Study
The objectives of the study are summarized in 5 stages. They are as mentioned below:
To identify and estimate the market size for the global cyber security market segmented by ccomponent, by ddeployment mmodel, by eenterprise ssize, by industry vvertical, region and by value (in U.S. dollars). Also, to understand the consumption/ demand created by consumers of cyber security between 2019 and 2031.
To identify and infer the drivers, restraints, opportunities, and challenges for the global cyber security market
To find out the factors which are affecting the sales of cyber security among consumers
To identify and understand the various factors involved in the global cyber security market affected by the pandemic
To provide a detailed insight into the major companies operating in the market. The profiling will include the financial health of the company's past 2-3 years with segmental and regional revenue breakup, product offering, recent developments, SWOT analysis, and key strategies.
Intended Audience
Research Methodology
Our research methodology has always been the key differentiating reason which sets us apart in comparison from the competing organizations in the industry. Our organization believes in consistency along with quality and establishing a new level with every new report we generate; our methods are acclaimed and the data/information inside the report is coveted. Our research methodology involves a combination of primary and secondary research methods. Data procurement is one of the most extensive stages in our research process. Our organization helps in assisting the clients to find the opportunities by examining the market across the globe coupled with providing economic statistics for each and every region. The reports generated and published are based on primary & secondary research. In secondary research, we gather data for global Market through white papers, case studies, blogs, reference customers, news, articles, press releases, white papers, and research studies. We also have our paid data applications which includes hoovers, Bloomberg business week, Avention, and others.
Data Collection
Data collection is the process of gathering, measuring, and analyzing accurate and relevant data from a variety of sources to analyze market and forecast trends. Raw market data is obtained on a broad front. Data is continuously extracted and filtered to ensure only validated and authenticated sources are considered. Data is mined from a varied host of sources including secondary and primary sources.
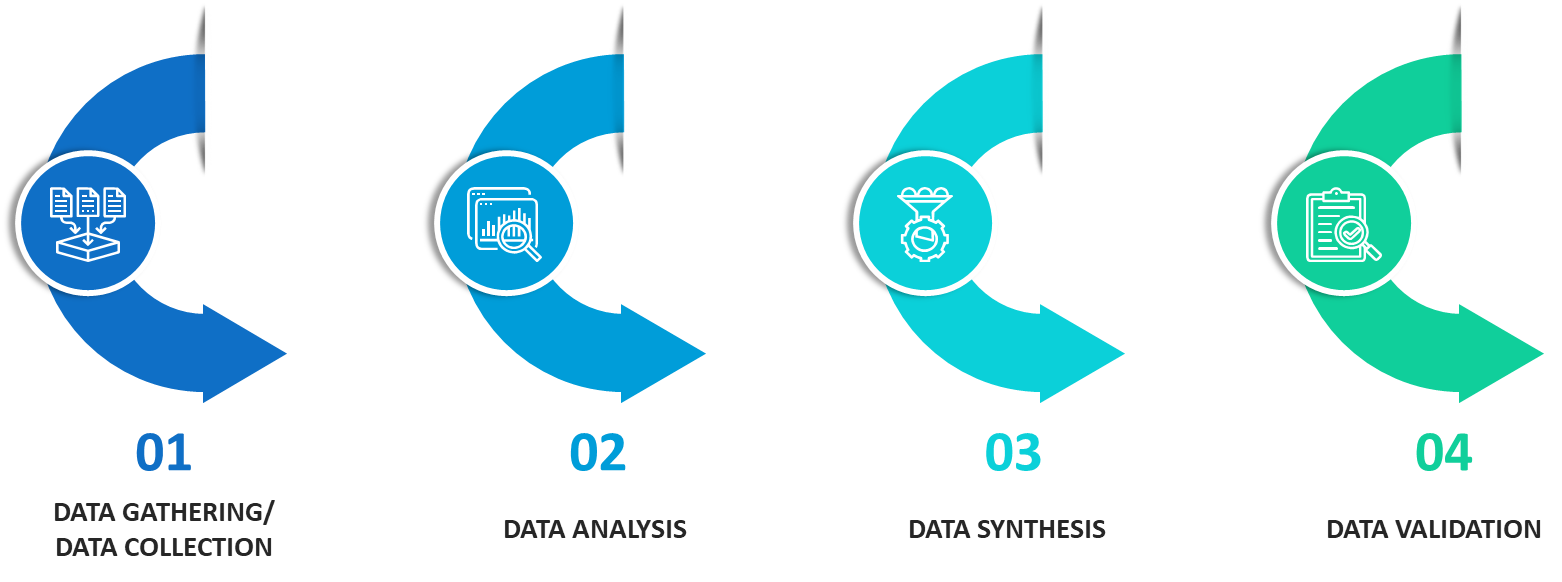
Primary Research
After the secondary research process, we initiate the primary research phase in which we interact with companies operating within the market space. We interact with related industries to understand the factors that can drive or hamper a market. Exhaustive primary interviews are conducted. Various sources from both the supply and demand sides are interviewed to obtain qualitative and quantitative information for a report which includes suppliers, product providers, domain experts, CEOs, vice presidents, marketing & sales directors, Type & innovation directors, and related key executives from various key companies to ensure a holistic and unbiased picture of the market.
Secondary Research
A secondary research process is conducted to identify and collect information useful for the extensive, technical, market-oriented, and comprehensive study of the market. Secondary sources include published market studies, competitive information, white papers, analyst reports, government agencies, industry and trade associations, media sources, chambers of commerce, newsletters, trade publications, magazines, Bloomberg BusinessWeek, Factiva, D&B, annual reports, company house documents, investor presentations, articles, journals, blogs, and SEC filings of companies, newspapers, and so on. We have assigned weights to these parameters and quantified their market impacts using the weighted average analysis to derive the expected market growth rate.
Top-Down Approach & Bottom-Up Approach
In the top – down approach, the Global Batteries for Solar Energy Storage Market was further divided into various segments on the basis of the percentage share of each segment. This approach helped in arriving at the market size of each segment globally. The segments market size was further broken down in the regional market size of each segment and sub-segments. The sub-segments were further broken down to country level market. The market size arrived using this approach was then crosschecked with the market size arrived by using bottom-up approach.
In the bottom-up approach, we arrived at the country market size by identifying the revenues and market shares of the key market players. The country market sizes then were added up to arrive at regional market size of the decorated apparel, which eventually added up to arrive at global market size.
This is one of the most reliable methods as the information is directly obtained from the key players in the market and is based on the primary interviews from the key opinion leaders associated with the firms considered in the research. Furthermore, the data obtained from the company sources and the primary respondents was validated through secondary sources including government publications and Bloomberg.
Market Analysis & size Estimation
Post the data mining stage, we gather our findings and analyze them, filtering out relevant insights. These are evaluated across research teams and industry experts. All this data is collected and evaluated by our analysts. The key players in the industry or markets are identified through extensive primary and secondary research. All percentage share splits, and breakdowns have been determined using secondary sources and verified through primary sources. The market size, in terms of value and volume, is determined through primary and secondary research processes, and forecasting models including the time series model, econometric model, judgmental forecasting model, the Delphi method, among Flywheel Energy Storage. Gathered information for market analysis, competitive landscape, growth trends, product development, and pricing trends is fed into the model and analyzed simultaneously.
Quality Checking & Final Review
The analysis done by the research team is further reviewed to check for the accuracy of the data provided to ensure the clients’ requirements. This approach provides essential checks and balances which facilitate the production of quality data. This Type of revision was done in two phases for the authenticity of the data and negligible errors in the report. After quality checking, the report is reviewed to look after the presentation, Type and to recheck if all the requirements of the clients were addressed.
